What to do with an email address in an investigation?
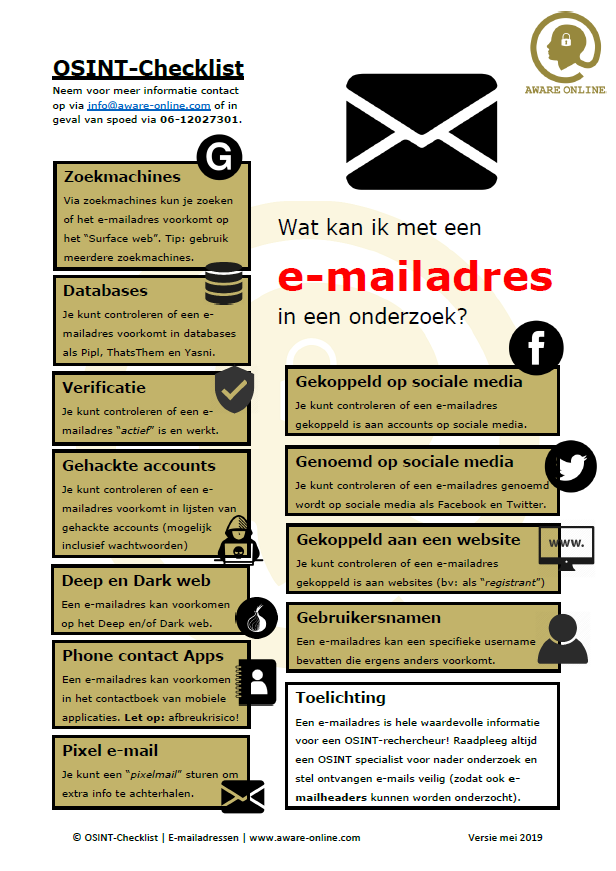
Imagine having an email address in your investigation: do you know what to do with it? There are so many OSINT tools available that it can be a bit overwhelming. For example, which tools do you use for verifying an email address? And how do you check whether an email address is associated with an account on social media? We will try to help you a little by providing you with an overview of steps that can be taken to investigate an email address.
OSINT Checklist: email addresses
Based on our own experience and the feedback of our students, we have created a couple of OSINT checklists. Every checklists focuses on the available information that you might be provided with. This can for example be an email address, a phone number a digital photograph.
Our checklists will point out WHAT steps you can be taken with the information present. The checklists In our OSINT tutorials and training events we will teach you HOW to take all investigative steps of our checklists. Below are a few examples.
Searching with search engines
With search engines you can check whether your target email address is present at the so called “surface web”. For example, when searching for “info@aware-online.com” on search engine Google, you will be presented with results of websites on which the email address is shown.
Due to the fact that search engines use their own crawler/spider/robot, the outcome of the search engines will be different. Please check multiple search engines and align your choice of a search engine with your target (where does he or she come from?).
Search engines like Google (globally), Yandex (Eastern-Europe) and Baidu (Asia) are very powerful. You might also want to have a look at meta search egines and clustering engines like Carrot2.
Searching the Deep Web
When one does not find an email address with an search engine, this does not necessarily mean that the email address is not used on the internet. This is because search engines only show results from the tip of the ice berg, the indexed information. Everything below the surface, the so called “Deep web“, is not indexed by surface web search engines.
Sounds exciting! Well, not really. Website administrators can manipulate the indexing process of search engines by search engines to not index their website. Website administrators can do this by specifying robots.txt files on their website. All information that is prohibited from indexing by search engines, is located in the Deep Web. Social media are often partly indexed but sometimes not at all.
When search engines do not lever you with the information that is needed, how do you search the Deep Web? Two ways to search the Deep Web are investigating databases and investigating social media that are partly indexed or not indexed at all. Please see our explanation below.
Searching social media
Can’t you find an email address by using search engines? Then you might need to move your investigation from search engines to the social media platforms. How to do this depends on the social media platform that you want to have a look at. On Facebook you can check whether an email address is mentioned by using the search bar and on twitter you can also directly fill in your target email address. By typing the target email address in the search bar, you are looking for stories (on Facebook) and Tweets (on Twitter) in which your target email address is mentioned.
Please always take a few minutes to think about your target. Your subjects age, place of birth and other details might be very relevant for the focus of your investigation. For example, social media platforms like Vkontakte, Nk.pl, Xing or Qzone can be the place to be for your investigation. Please make sure to not forget social media platforms like Skype, YouTube and Spotify. Every social media platform has other ways to effectively search for information on.
Searching databases
When searching with search engines does not yield any results, you might want to take a look at (commercial) databases such as Pipl, Yasni and ThatsThem. It is not always completely transparent how databases such as the databases above collect their data, but the data present can be of importance. Please make sure to verify all results because information might be outdated or even incorrect.
Tip: some databases and services provide you with better results when using the Application Programming Interface (API) or a paid license. The use of API’s sometimes is free of charge and it can provide you with better results than the regular searching within the database.
Searching hacked email addresses
Regular search engines will sometimes show you hacked account details such as email address and passwords. However, there are better ways to search for hacked email addresses.
Websites that can be used to search for hacked email addresses are HaveIBeenPwned, Dehashed (paid) and Pastebin. These websites will show you whether an email address has been compromised by which breach and which account details can be found publicly on the internet.
This provides you with insight in the accounts and services that might be used by your target, in what passwords are used and in if there are any other email accounts that are associated with that same password.
Is an email address associated with an account on social media?
Email addresses are very interesting pieces of an OSINT puzzle for almost every investigator, researcher or analyst. With email address one might find out if there are any accounts on social media associated with the email address. The way to check this depends on the social media platform you want to investigate.
A couple of weeks ago, we have written a blog post about how to find an Twitter account with just an email address. And with the following custom Email Search Tool you can find out if an email address is associated with an account on LinkedIn:www.linkedin.com/sales/gmail/profile/viewByEmail/info@aware-online.com.
We will publish more blog post about finding accounts on social media by looking at an email address soon. Android Emulators and mobile applications play a key role.
Searching via phone contact Apps
There are numerous Phone Contact Apps available that might help you find out the owner of an email address. Aric Toler published a great blog post at Bellingcat about these type of contact apps that can be used for phone number investigations.
Please be careful: whenever using Phone Contact Apps, your contacts might be uploaded to the database of the application. Therefore, always use a “clean” cellphone (or Android emulator).
Is an email address associated with a website?
Another option is to check wether an email address is registerd in the WHOIS data of a website. At the registration of domain names and websites, details about the owner of a domain name (the registrant) and about the hosting provider (the registrar) will be registered. Therefore, you can check whether an email address is used for the registration of a domain name or website or for the contact details of the technical contact person. Websites that might help you with this investigation are DomainBigData and Whoxy.
How to verify an email address?
When looking at an email address, how do you know if the email address is still in active or not? There are different tools available that can help you with this. For example, try Mailtester or Hunter.
From email address to username?
In some cases, you can derive an username from an email address. Image we are using the email address “AO_1987@gmail.com” for communication with our students and clients. Or username might in that case be “AO_1987”, which username also might be used for other email addresses (“AO_1987@hotmail.com”, “AO_1987@outlook.com”, etcetera) or for accounts on social media (Facebook, Instagram, etcetera). You will need to verify whether the email addresses found are traceable to your target email address.
A pixel email?
Have you ever heard of a “pixel email“. A pixel email is actually an email that you send to a target email address in order to retrieve information such as an IP address of your target. Please always check whether your are allowed to send a pixel email (probably not!). Arnoud Engelfriet wrote an interesting blog post about this back in 2017.
Email addresses and the Dark Web
Besides the Surface Web and the Deep Web, email address might be present at the Dark Web as well. The Dark Web is the part of the internet that is not indexed by surface web crawlers and where “special” software like the TOR browser is needed to access it. Because the Dark Web is hardly indexed, searching for information like an email address can be very difficult. Within this blog post we do not publish any links to so called “Hidden Services” because we cannot guarantee that those services are “safe”.
Please always adhere to laws and regulations in your investigation.
Links to third-party websites are placed in this blog post. Aware Online is in no way responsible for the use of these links. The use of links on this page is therefore entirely at your own risk.
More tutorials or contact?
Do you want to know more about how you can investigate email addresses? Sign up for one of our OSINT training events or contact one of our specialists . Do you have any comments or additions to this article? Please let us know!